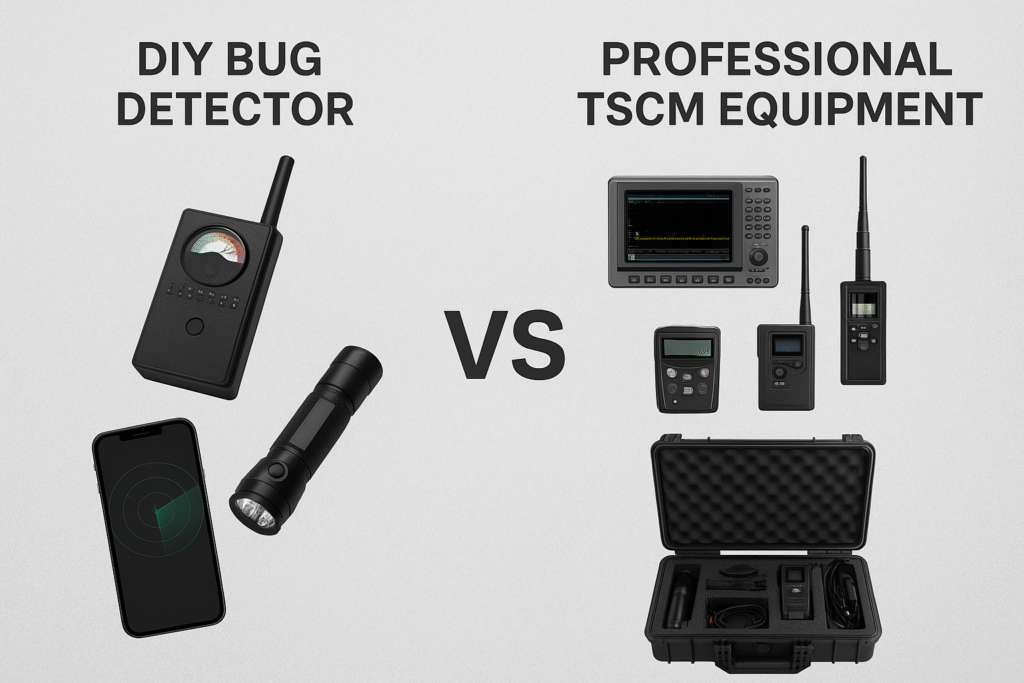
DIY Bug Sweep Equipment vs Professional Services
Compact spy tech, hybrid work, and ubiquitous IoT have made confidential spaces easier to compromise. DIY bug sweep gadgets promise quick peace of mind—but professional Technical Surveillance Counter‑Measures (TSCM) deliver evidence‑backed answers. Here’s how to decide which approach fits your risk, budget, and timeline. This article is for general education, not legal advice. Surveillance and […]
DIY Bug Sweep Equipment vs Professional Services Read More »